Secure Customer Data With HTTPS and SSL
If your store doesn’t use HTTPS, visitors see a warning before they even reach your homepage. That alone is enough to lose a sale. Beyond first impressions, unsecured websites leave customer data exposed to interception.
HTTPS protects your site by encrypting data as it moves between your customer’s browser and your server. It only works if your store has an SSL certificate installed.
Why This Matters
-
Visitors notice the padlock icon in the address bar. Without it, trust drops.
-
Sensitive information stays encrypted, including passwords and credit card details.
-
Search engines prefer HTTPS, so your rankings may improve.
-
Payment processors often require it before approving transactions.
How to Set It Up
-
Start with your hosting provider. Most include a free SSL certificate from Let’s Encrypt.
-
Need stronger validation? Providers like DigiCert and Sectigo offer paid options with added verification.
-
Redirect all traffic to HTTPS. This ensures every page is protected and avoids SEO issues from duplicate content.
Switching to HTTPS isn’t optional it’s a basic requirement for any store that accepts payments or collects personal data. It’s one of the few security upgrades that directly influences both trust and conversions.
Keep Your Software and Plugins Updated
Outdated code is one of the easiest ways in for attackers. If your store runs on old software or extensions, you’re likely missing security patches that fix known vulnerabilities.
Even small delays in updates can expose your site. Hackers often scan for unpatched systems to exploit. Staying current reduces this risk.
What Needs Regular Updating
-
Your eCommerce platform. Whether you use OpenCart, WooCommerce, or another system, check for version updates and security fixes.
-
Themes and extensions. These often rely on third-party code, which can be a target if left unpatched.
-
Server software. PHP, MySQL, and other backend tools also need to be kept current.
How to Stay Ahead
-
Set a routine. Schedule weekly or monthly checks for available updates.
-
Use test environments. Try updates in a staging setup first to catch issues before applying them to your live store.
-
Turn on automatic updates when available, especially for minor patches and security releases.
Updating isn’t just about features it’s about closing doors that shouldn’t stay open. A secure store starts with current software across every layer.
Use a Secure eCommerce Platform
The platform you choose is the foundation of your store’s security. If it lacks key protections or if support is slow to respond your store could be exposed before you even notice there’s a problem.
A secure eCommerce platform handles the heavy lifting: user authentication, data encryption, and compliance standards. The right choice limits your risk from day one.
What to Look for in a Secure Platform
-
Regular security updates. The platform should have a clear track record of patching vulnerabilities quickly.
-
Two-factor authentication for admins. This adds a critical layer of login protection.
-
Built-in protections. Look for options like password hashing, permission controls, and CAPTCHA to guard login and checkout pages.
-
Active support and community. A responsive developer team and a large user base often lead to faster fixes and better solutions.
Examples of Platforms That Prioritize Security
-
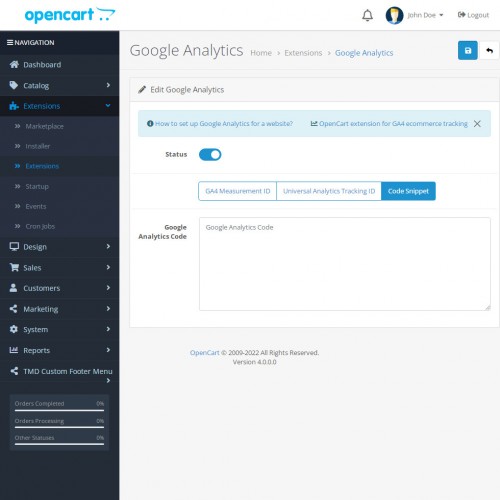
OpenCart. Offers solid baseline security features, regular updates, and a wide extension marketplace. Admin access can be restricted by IP, and extensions are available to add extra security layers.
-
Shopify. A hosted solution with built-in SSL, PCI compliance, and fraud analysis tools.
-
Magento (Adobe Commerce). Best suited for developers with strong security needs; offers advanced configuration options and granular access controls.
Before You Commit
-
Check the update history. Long gaps between releases can indicate slow responses to known issues.
-
Review user forums. Recurring complaints about bugs or downtime are red flags.
-
Test basic protections. Try creating weak passwords or submitting forms without CAPTCHA to see what the platform allows by default.
Your platform sets the tone for how secure your store can be. Choose one that’s actively maintained and built with protection in mind so you’re not constantly plugging holes later.
Implement Strong Authentication Practices
Weak login credentials are one of the most common points of failure in online stores. If an attacker can access your admin panel or customer data with a simple password, every other security measure becomes irrelevant.
Strengthening authentication reduces that risk by making unauthorized access far more difficult.
Passwords Alone Aren’t Enough
-
Require complex passwords. Set minimum requirements for length, numbers, symbols, and case variation. Avoid allowing common passwords like “admin123” or “password1.”
-
Enforce regular password updates. This can limit damage if credentials are ever compromised.
-
Avoid shared logins. Each staff member should have their own account with the least access necessary.
Add Two-Factor Authentication (2FA)
-
Enable 2FA for admin accounts. A one-time code sent to an email or app adds a second layer of protection beyond a password.
-
Use app-based 2FA if possible. Authenticator apps are harder to intercept than email or SMS.
-
Apply 2FA to customer logins where appropriate. Especially for high-value accounts or B2B portals.
Control Access to the Admin Area
-
Change the default admin URL. Attackers often target known login paths like
/adminor/wp-admin. -
Limit login attempts. Set a cap to prevent brute-force attacks.
-
Restrict access by IP. Only allow known addresses to reach your admin panel, if your hosting setup supports it.
Strong authentication isn’t only about keeping outsiders out it’s also about preventing accidental mistakes from within. A secure login process protects both your store and your team.
Secure Payment Gateways
Customers trust your store with their most sensitive information credit card numbers, billing details, and contact data. If your payment process is not secure, that trust can disappear instantly.
The safest approach is to avoid handling card data yourself. Instead, use a payment gateway that specializes in secure processing and meets strict industry standards.
Choose a PCI-Compliant Provider
-
Look for PCI DSS compliance. This standard ensures that the provider follows strict security rules for storing, processing, and transmitting cardholder data.
-
Verify certification. Providers should clearly list their PCI status on their websites or documentation.
Avoid Storing Payment Information
-
Use tokenization. Many gateways replace card details with a secure token, which removes the need to store sensitive data on your servers.
-
Disable card storage unless necessary. If you must offer saved cards, be clear with users and apply extra authentication.
Protect the Payment Flow
-
Use embedded or redirected checkouts. Hosted checkout pages, like those offered by Stripe or PayPal, shift the responsibility for security to the gateway.
-
Watch for fake forms. Ensure that custom checkout pages aren’t vulnerable to code injection or content tampering.
Monitor for Irregular Activity
-
Enable fraud detection tools. Many providers offer built-in systems to flag suspicious behavior, such as rapid-fire transactions or mismatched billing data.
-
Log and review payment errors. Failed transactions or chargebacks can indicate deeper issues worth investigating.
A secure gateway reduces both risk and liability. Letting a trusted provider handle payments gives customers peace of mind and helps you stay focused on running your store.
Regular Backups and Recovery Plans
A security breach can take your store offline in seconds. If you don’t have a recent backup or a clear recovery plan getting back online could take days or longer.
Backups are your safety net. When configured correctly, they can help restore lost data, fix broken systems, or undo damage from an attack.
What to Back Up and How Often
-
Database contents. This includes customer records, orders, products, and settings. It should be backed up daily.
-
Site files and configurations. Code, themes, images, and plug-ins should be backed up regularly at least weekly, or after every major update.
-
Logs and admin activity. These are useful for identifying what happened in the lead-up to a problem.
Best Practices for Backup Storage
-
Use offsite or cloud storage. Avoid storing backups on the same server as your website. If the server is compromised, so is your backup.
-
Automate the process. Schedule backups to run without manual input to avoid gaps or forgotten steps.
-
Keep multiple versions. Store at least three recent backup versions in case the latest one contains errors or malware.
Have a Plan for Recovery
-
Test your backups. A backup is only useful if it works. Run test restores on a staging site to confirm integrity.
-
Document the recovery steps. Create a clear, step-by-step guide on how to bring your store back online if something goes wrong.
-
Assign responsibilities. Know who handles recovery and how to contact them quickly.
A backup plan isn’t just about copying files. It’s about preparation. When things go wrong, how fast you recover depends on how well you planned ahead.
Use a Web Application Firewall (WAF)
Many attacks don’t start with a full breach. They begin with small, automated probes looking for weaknesses in your site’s forms, login pages, or URLs. A Web Application Firewall (WAF) blocks this traffic before it reaches your store.
Unlike traditional firewalls that protect networks, a WAF filters HTTP traffic. It helps stop threats like cross-site scripting, SQL injection, and malicious bots without requiring changes to your website code.
What a WAF Can Do
-
Block known attack patterns. WAFs use signature-based rules to identify and reject suspicious behavior in real time.
-
Filter bad bots. These include scrapers, fake checkout bots, and tools that test stolen credit cards.
-
Inspect user inputs. WAFs monitor data submitted through contact forms, login fields, and search bars.
-
Limit brute-force attempts. Repeated login attempts from the same IP can be flagged or blocked.
Options for eCommerce Stores
-
Cloud-based WAFs. Services like Cloudflare, Sucuri, and AWS WAF don’t require installation. They sit between your site and your users, analyzing every request.
-
Plugin-based WAFs. Some platforms offer modules or extensions for firewall protection. These work within your store but may use server resources.
-
Managed hosting firewalls. If you use a managed hosting provider, check if WAF protection is already included.
Setup and Maintenance Tips
-
Start with default rulesets. Most WAF tools offer preconfigured settings that block common attacks.
-
Whitelist trusted services. Make sure legitimate tools (like payment gateways or marketing integrations) aren’t accidentally blocked.
-
Review firewall logs. Regularly check for denied requests to understand what’s being blocked—and why.
A WAF acts as your store’s front line of defense. By filtering out dangerous traffic before it reaches your site, it protects both your data and your customers.
Limit Access and Use Role-Based Permissions
Not every team member needs full access to your store’s backend. Granting broad permissions increases the risk of accidental errors or worse, internal misuse.
A role-based approach helps control what each user can see and do, minimizing unnecessary exposure to sensitive areas.
Assign Roles Based on Job Function
-
Create defined roles. Separate roles for customer support, content editing, inventory, and administration help you manage access more precisely.
-
Avoid using admin accounts for daily tasks. Reserve high-level permissions for specific tasks like updates or configuration changes.
-
Deny access by default. Start with limited permissions, then add only what’s needed for each user.
Review and Adjust Access Regularly
-
Audit user accounts monthly. Remove access for former employees or temporary contractors.
-
Check for unused accounts. If a login hasn’t been used in weeks, consider disabling it.
-
Update roles when responsibilities change. Don’t let outdated access carry over to new roles.
Use Platform Features to Control Access
-
Look for built-in permission settings. Most platforms let you create user roles and assign access to modules or features.
-
Log all admin actions. Enable logging to track who made changes, when, and from where.
-
Restrict access by IP if possible. This adds an extra layer of control, especially for sensitive functions.
Controlling access isn’t just about trust it’s about limiting opportunities for mistakes. Fewer people with fewer privileges means fewer ways things can go wrong.
Monitor and Scan for Threats
Security tools can’t help you if you’re unaware something’s wrong. Many breaches go undetected for weeks giving attackers time to steal data, modify files, or plant hidden malware.
Continuous monitoring and regular scans help you catch problems early and respond before they escalate.
Set Up Real-Time Monitoring
-
Track admin activity. Record logins, changes to settings, and content edits. Look for unfamiliar IP addresses or behavior outside normal hours.
-
Use error and access logs. These provide clues about failed login attempts, unusual traffic spikes, or blocked pages.
-
Monitor uptime and file integrity. Tools that alert you to site downtime or unexpected changes in core files can catch signs of tampering.
Scan for Malware and Vulnerabilities
-
Run malware scans regularly. Schedule them daily or weekly depending on your store’s size and traffic.
-
Check for outdated software. Vulnerability scanners can flag known issues in themes, plugins, and platform versions.
-
Inspect for suspicious code. Look for unauthorized scripts, hidden redirects, or modified checkout processes.
Tools and Services to Consider
-
Security plugins. Many eCommerce platforms offer scanning tools through extensions or built-in options.
-
External scanners. Use services like Sucuri SiteCheck or Detectify to scan from outside your environment.
-
Hosting-level tools. Some hosting providers include security dashboards that combine logs, scans, and alerts in one place.
Monitoring doesn’t stop attacks but it gives you a head start when they happen. The faster you notice an issue, the more control you have over the outcome.
Educate Your Team
No matter how secure your software is, people remain a common entry point for attacks. A single click on a fake email or a careless password can expose your entire store.
Training your team to recognize threats and handle data responsibly is just as important as any technical fix.
Focus on Common Threats
-
Phishing scams. Teach staff to spot fake emails asking for logins or sensitive information. Show examples and test occasionally.
-
Suspicious links and attachments. Encourage a rule: don’t open anything unexpected without confirming the source.
-
Password habits. Reinforce the use of strong, unique passwords and discourage sharing credentials between users.
Make Security Part of Onboarding
-
Start with basic principles. New hires should understand how their role connects to store security.
-
Explain internal tools and protocols. If you use specific apps for file sharing, communication, or access management, make sure staff knows the rules.
-
Use real examples. Share incidents (from your store or others) to show how simple mistakes can lead to major problems.
Keep Security Top of Mind
-
Send regular reminders. A short monthly email with tips or updates keeps security visible.
-
Run simulated threats. Tools that mimic phishing attempts can help identify training gaps.
-
Encourage questions. Create a space where employees feel comfortable reporting suspicious activity even if they’re unsure.
Security is a shared responsibility. When your team understands how to protect the store—and feels confident doing it you lower the risk across the board.
Conclusion: Build Security Into Your Store’s Routine
Security isn’t a one-time setup. It’s an ongoing habit that protects your store as it grows and as threats evolve.
Every safeguard covered in this guide works best when it becomes part of your regular process. Updates, training, monitoring, and access controls all rely on consistency to be effective.
Key Takeaways
-
Use HTTPS to protect data in transit and build customer trust.
-
Keep all software updated to prevent known exploits from being used against you.
-
Choose a secure platform with active support and built-in protections.
-
Strengthen authentication to guard against unauthorized access.
-
Rely on trusted payment gateways to handle sensitive financial data.
-
Create backups and test your recovery plan before you need it.
-
Install a WAF to block threats before they hit your store.
-
Limit user access to reduce the chances of internal errors or misuse.
-
Monitor for threats so you can act quickly when issues arise.
-
Train your team to recognize and respond to security risks.
There’s no single fix for every threat. But by following these steps and sticking to them you create a store that’s prepared, not reactive. That preparation protects your business, your data, and your customers every day.